
A new Mac malware named “Realst” is being used in a massive campaign targeting Apple computers, with some of its latest variants including support for macOS 14 Sonoma, which is still in development.
The malware, first discovered by security researcher iamdeadlyz, is distributed to both Windows and macOS users in the form of fake blockchain games using names such as Brawl Earth, WildWorld, Dawnland, Destruction, Evolion, Pearl, Olymp of Reptiles, and SaintLegend.
These games are promoted on social media, with the threat actors using direct messages to share access codes required to download the fake game client from associated websites.
Access codes allow the threat actors to vet those they wish to target and avoid security researchers who want to reveal malicious behavior.
In reality, the game installers infect devices with information-stealing malware, such as RedLine Stealer on Windows and Realst on macOS. This type of malware will steal data from the victim’s web browsers and cryptocurrency wallet apps and send them back to the threat actors.

Source: iamdeadlyz.gitbook.io
SentinelOne analyzed 59 Mach-O samples of the Realst malware found by iamdeadlyz, focusing on its macOS versions, and found several distinct differences.
This allowed the researchers to identify 16 variants of the macOS malware, a sign of active and rapid development.
The Realst Mac malware
When downloading the fake game from the threat actor’s site, they will be offered either Windows or macOS malware, depending on their OS.
The Windows malware is typically RedLine Stealer, but sometimes other malware like Raccoon Stealer and AsyncRAT.
For Mac users, the sites will distribute the Realst info-stealing malware, which targets Mac devices as PKG installers or DMG disk files containing the malicious Mach-O files but no real games or other decoy software.
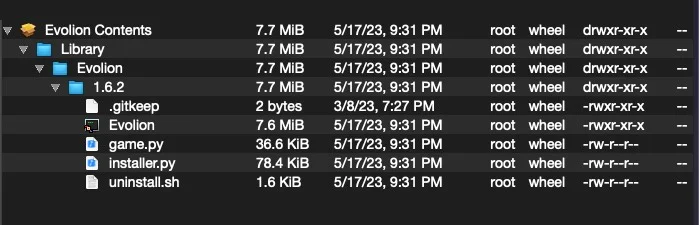
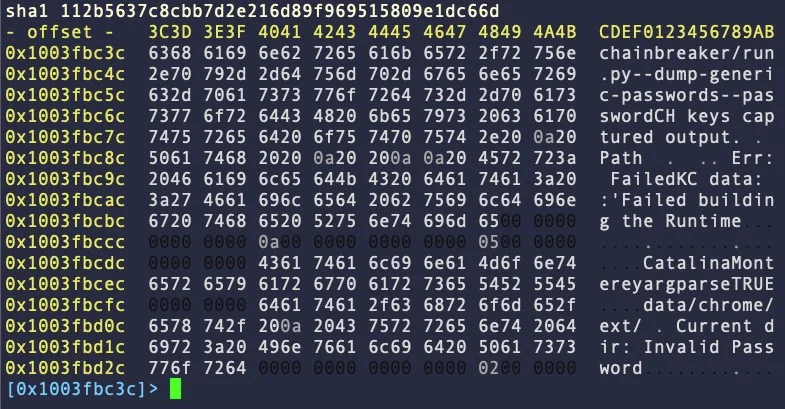
The “game.py” file is a cross-platform Firefox infostealer and “installer.py” is “chainbreaker,” an open-source macOS keychain database password, keys, and certificates extractor.
SentinelOne found that some samples are codesigned using valid (now revoked) Apple Developer IDs, or ad-hoc signatures, to bypass detection from security tools.
The variants
All 16 distinct Realst variants analyzed by SentinelOne are fairly similar in form and function, although they utilize different API call sets.
In all cases, the malware targets Firefox, Chrome, Opera, Brave, Vivaldi, and the Telegram app, but none of the analyzed Realst samples target Safari.
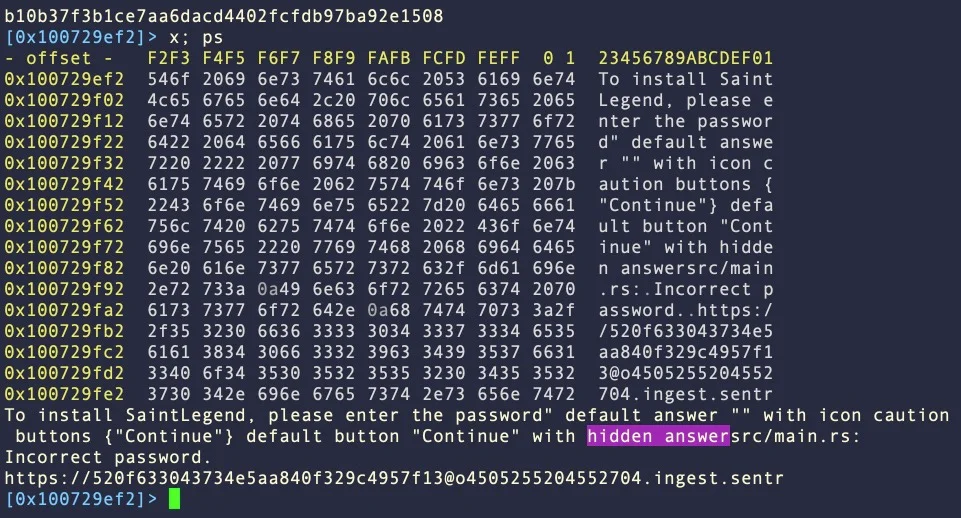
“Most variants attempt to grab the user’s password via osascript and AppleScript spoofing and perform rudimentary checking that the host device is not a virtual machine via sysctl -n hw.model,” explains SentinelOne in the report.
“Collected data is dropped in a folder simply named “data” [which] may appear in one of several locations depending on the version of the malware: in the user’s home folder, in the working directory of the malware, or in a folder named after the parent game.”
The 16 distinct variants are categorized into four main families based on their traits, namely A, B, C, and D.
Family A, which has the most samples in circulation, uses “AppleScript spoofing” to trick the victim into typing their admin password on a dialog box.
Family B is similar to A and also uses password spoofing but divides the relevant strings into smaller units to evade simple static detection.
Family C also has a reference to chainbreaker within the binary itself, which allows it to extract data from the system’s keychain database.
Finally, Family D uses the Terminal window to prompt the victim to enter their password, which is used to dump saved credentials stored in Keychain.
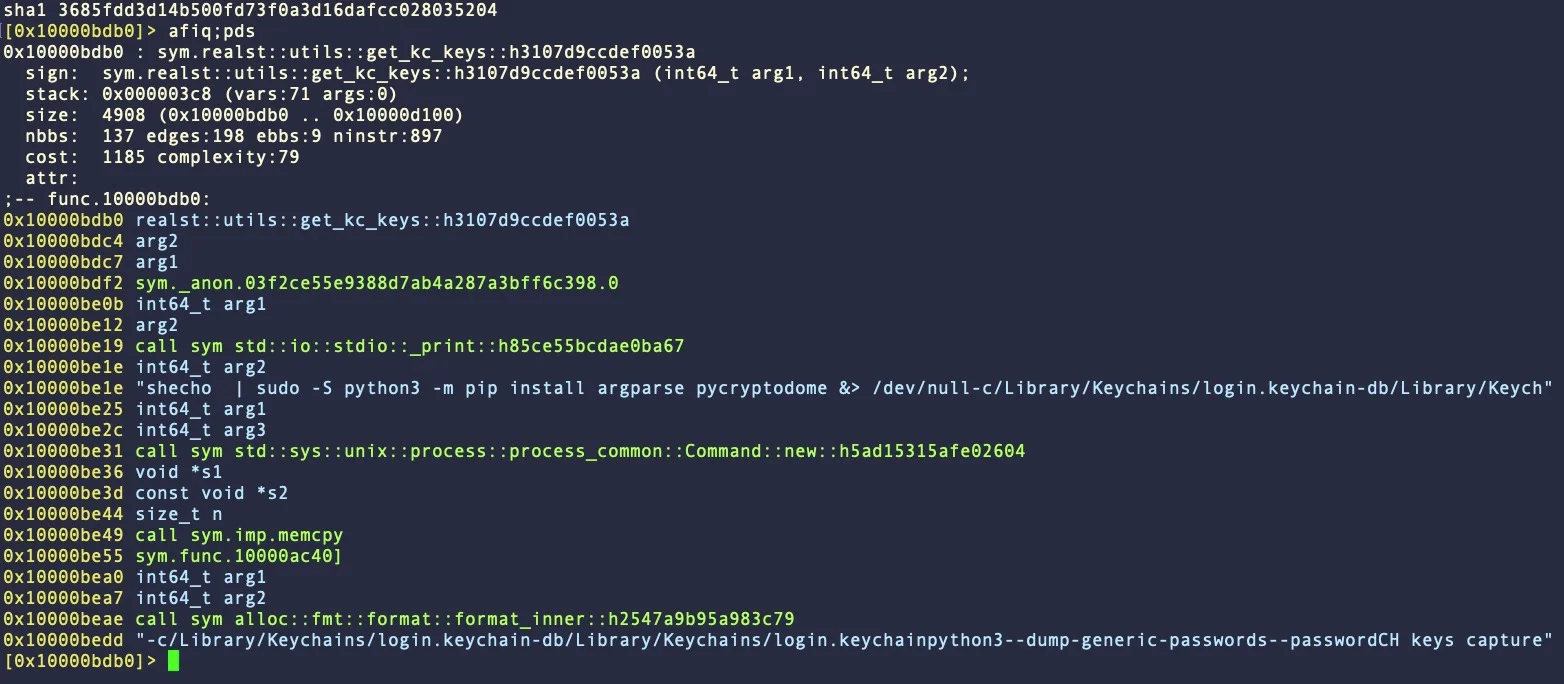
In some cases, Family D leverages the acquired password to gain admin privileges on the system and install the Python cryptography library “pycryptodome,” which is also used to dump credentials from the Keychain.
Roughly 30% of the samples from families A, B, and D contain strings that target the upcoming macOS 14 Sonoma.
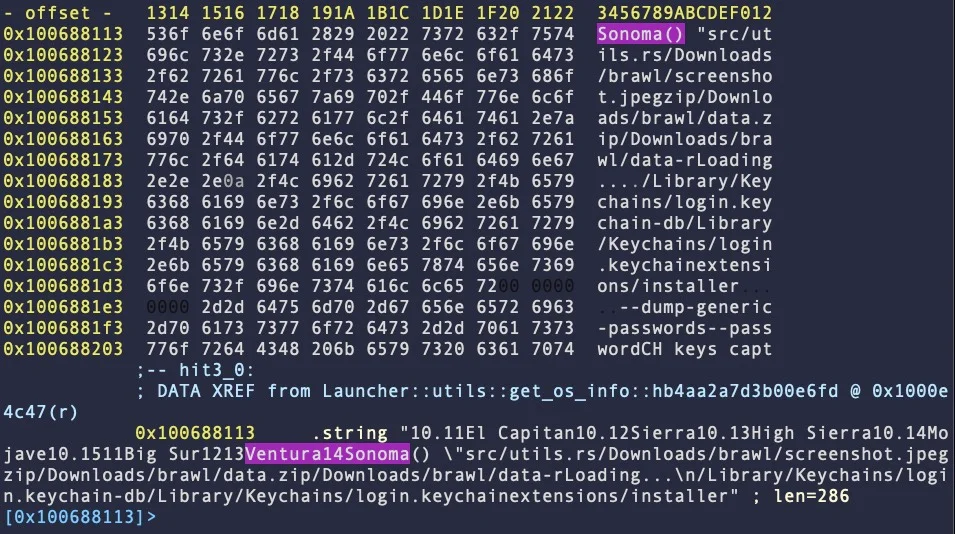
The presence of those strings shows that the malware authors are already preparing for Apple’s forthcoming desktop OS release, ensuring that Realst will be compatible and working as expected.
MacOS users are advised to be cautious with blockchain games, as those distributing Realst use Discord channels and “verified” Twitter accounts to create a false image of legitimacy.
Furthermore, as these games specifically target cryptocurrency users, the main goal is likely to steal crypto wallets and the funds within them, leading to costly attacks.