
Hacktivist groups that operate for political or ideological motives employ a broad range of funding methods to support their operations.
Israeli cyber-intelligence firm KELA notes that although hacktivism appears to be about causing service disruption through DDoS attacks or reputation damage via data leaks, the modus operandi of these threat groups encompasses a broader scope of activities, including common cybercrime tactics.
These tactics include stealing and selling data, selling malware and botnet licenses, demanding ransom from victims, or even offering hack-for-hire services aimed at targets with no political significance.
Going beyond donations
Starting with the pro-Russia group Killnet, KELA says the hacktivists promoted a botnet for hire in November 2021, but their monetization methods expanded significantly in 2023.
Killnet set up a hack-for-hire service in March 2023, announced a new DDoS-for-hire service in July 2023, and launched a ‘Dark School’ training program selling nine hacking courses to interested hackers in May 2023.
Also in May, as the group’s following grew on Telegram, Killnet announced a cryptocurrency exchange platform that charged a service rate between 3-4%.
Between November 2022 and April 2023, Killnet was observed attempting to sell logs, data, and access to networks on their Telegram channels and the Infinity forum, which is owned and operated by the group and also features advertisements.
Finally, Killnet has attempted to extort victims into paying ransom to stop DDoS attacks or delete stolen data, like in the case of RuTor in August 2022, BlackSprut in November 2022, the Latvian government in November 2022, and NATO in April 2023.
Anonymous Russia, another pro-Kremlin hacktivist group, has also displayed monetization activities beyond politically-motivated DDoS attacks targeting European countries.
In April 2023, the group switched from requesting donations to launching paid services like the Tesla botnet malware advertised on the group’s Telegram channel.
In May 2023, Anonymous Russia announced the launch of a new DDoS service to target Tor sites, clearly aiming at clients from the dark web space.
Next is Phoenix, also a pro-Russian DDoS group that initially launched as a sub-team of Legion and which quickly adopted alternative monetization methods like selling stolen data on Telegram starting in March 2023.
Claimed victims of Phoenix who were openly extorted on the group’s Telegram channel include the law firm Michele Bonetti and the telecom firm Cellular Pacific.
The group’s leader has also stated that they privately offer DDoS-for-hire services, while he delivers personal hacker training courses via Telegram for a fee of up to $2,675.
In April 2023, Phoenix announced they would begin video and audio streaming their attacks, allowing the highest bidder access to the live stream.
Anonymous Sudan, a hacktivist group that emerged in January 2023 and has documented ties with Killnet, also sells stolen data on their Telegram channel, according to KELA.
In March 2023, the group attempted to sell what they claimed to be data stolen from Air France for $3,000, while they demanded a payment of $3,500 from Scandinavian Airlines (SAS) to stop the attacks.
In June 2023, Anonymous Sudan announced they had attacked Microsoft and demanded a payment of $1,000,000 to stop the DDoS attacks that crippled the firm’s services.
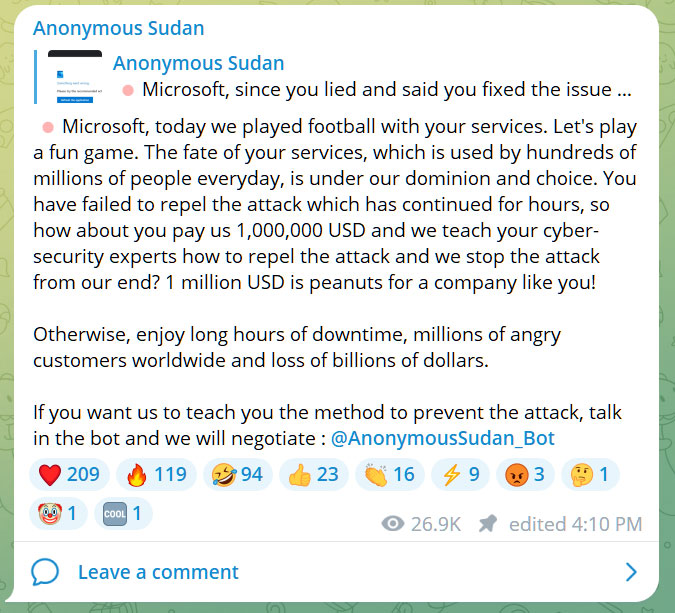
Source: BleepingComputer
In July 2023, they advertised the sale of a database supposedly containing the data of 30 million Microsoft accounts for $50,000.
Arvin Club is a hacktivist group fighting against the Iranian regime by launching DDoS attacks against government ministries and organizations, active since 2019.
In April 2023, the group launched a private subscription-based ($49) Telegram channel to sell data stolen from their attacks, newest exploits and vulnerabilities, and more.
Finally, KELA’s report highlights the pro-Russian hacktivist group Passion, which emerged in December 2022 using its own botnet to attack Ukrainian organizations.
Mere days after the group’s launch that botnet was offered for sale starting at $30/week, while the newest version that is also available for purchase was announced in March 2023.
Not to be treated lightly
KELA believes these hacktivist groups are monetizing their operations mainly to stay active and continue launching powerful attacks at their target. However, regardless of their funding, it does not make them less dangerous to internet users and organizations.
For example, in early June, Microsoft suffered several outages against the web portal for Azure, Microsoft OneDrive, and Microsoft Outlook.
While Anonymous Sudan claimed credit for the attacks during this period, it wasn’t until ten days later that Microsoft finally admitted that their services were disrupted in DDoS attacks, illustrating the damaging potential behind hacktivists groups.
The consequences of data theft and the exposure of sensitive information remain significant regardless of whether they are primary or secondary objectives.
While some researchers consider these hacktivist groups low-level threat actors due to their damage potential and business disruption, it may be wiser to consider them in the same light as regular cybercriminals.