Etiket: SSM
AWS VDP, Nick_FRICHETTE_DD tarafından gönderilen bir hatayı açıkladı: https://hackerone.com/reports/2926361 Source link
08 Nisan 2025Ravie LakshmananBulut Güvenliği / Güvenlik Açığı Siber güvenlik araştırmacıları, Amazon EC2 Simple System Manager (SSM) ajanında, başarılı bir…
Cisco, saldırganların yama uygulanmamış Cisco Smart Software Manager On-Prem (Cisco SSM On-Prem) lisans sunucularındaki tüm kullanıcı parolalarını değiştirmesine olanak tanıyan…
Cisco, Cisco Smart Software Manager On-Prem lisanslama aracında bulunan ve saldırganların lisans sunucularındaki yöneticiler de dahil olmak üzere herhangi bir…
Cisco, saldırganların Güvenli E-posta Ağ Geçitlerindeki dosyaların üzerine yazmasına (CVE-2024-20401) ve Akıllı Yazılım Yöneticisi Yerinde lisans sunucularındaki herhangi bir kullanıcının…
Cisco, saldırganların Cisco Smart Software Manager On-Prem (Cisco SSM On-Prem) lisans sunucularındaki yöneticiler de dahil olmak üzere herhangi bir kullanıcının…
İşte geçen haftanın en ilginç haberlerinden, makalelerinden, röportajlarından ve videolarından bazılarına genel bir bakış: Açık kaynak penetrasyon testi aracı BloodHound…
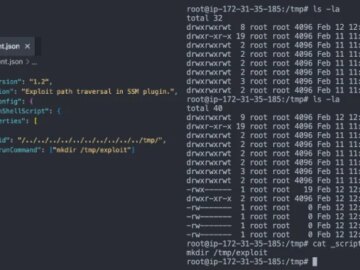
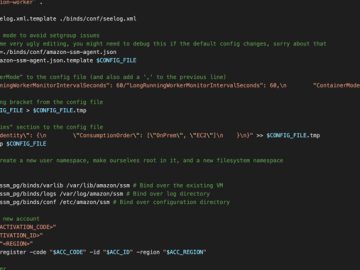
Legitimate SSM agents can turn malicious when attackers with high-privilege access use it to carry out ongoing malicious activities on…
Amazon Web Services (AWS) has a novel post-exploitation approach that has been identified by researchers. This technique enables hackers to…
Mitiga researchers have documented a new post-exploitation technique attackers can use to gain persistent remote access to AWS Elastic Compute…
Researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS) that allows hackers to use the platform’s System…
Aug 02, 2023THNCloud Security / Cyber Threat Cybersecurity researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS)…