Kategori: CyberSecurityNews
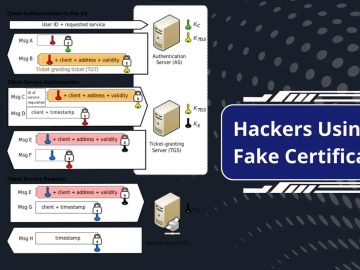
Saldırganlar, sahte sertifikalar kullanarak kurumsal ağ kaynaklarına yetkisiz erişim elde eder. Saldırganlar, Anahtar Dağıtım Merkezini (KDC) hedef şirketin ağına girmesi…
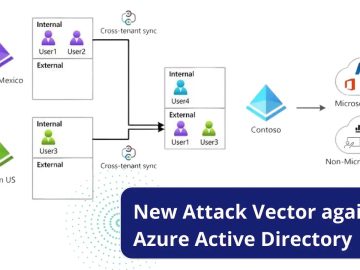
Gelen haberlere göre, SolarWinds saldırılarından sorumlu olan ve “Nobelium” olarak bilinen tehdit grubunun, Microsoft tarafından kullanıma sunulan yeni Kiracılar Arası…
Bilgisayar korsanları, LOLBAS’tan (Living-Off-the-Land Binaries-And-Scripts) aktif olarak yararlanır; bu, tehdit aktörleri tarafından gerçekleştirilen yasa dışı eylemleri gizlemek için yasal araçlardan…
Tehdit aktörleri, tekniklerini ve araçlarını, mevcut tehdit senaryosunu tamamen değiştiren bir hızla geliştiriyor. BlueCharlie, 2017’den beri aktif olan ve aşağıdakiler…
There is a critical vulnerability in Ivanti’s MobileIron Core 11.2 version that could allow a malicious actor to gain unauthorized…
Hackers exploited a zero-day vulnerability in the email services and SMTP servers of Salesforce. Malicious email traffic is often concealed…
Google has published a security update for Chrome, updating the Stable channel for Mac and Linux to 115.0.5790.170 and 115.0.5790.170/.171 for…
Microsoft Threat intelligence identifies Midnight Blizzard (previously tracked as NOBELIUM) as a highly targeted social engineering attack. The attacker uses…
There have been several reports recently about cybercriminals using AI-powered tools for malicious purposes which can give a paradise of…
SpecterOps announced BloodHound Community Edition (CE), which will be available in early access on August 8, 2023! SpecterOps is a…
A new phishing tactic was discovered that takes advantage of Google Accelerated Mobile Pages (AMP), which is known to be…
The potentially unaware C2P entities that serve as legit businesses could be exploited easily by threat actors for attack campaigns…